-

Unravelling the roles: Software Engineer, Developer, Scientist
The skills required for the creation of software is one that anyone can gain. Literally, you, your parents, your friends, your children, anyone can learn. It is not a magical skill set, and can be self-taught with little more than an internet connection and the desire to solve problems. Whilst universities and boot camps are…
-

Pesto
After picking your basil, check it for friends of the garden like this frog, or spiders. Return the friends to the garden and wash the basil. One year, I grew so much basil that we made about 1kg of pesto. The freezer was full of a lot of small containers of pesto that we thawed…
-

Data Repository – A design pattern for data storage – Part 1
Data storage in applications is a complex task that requires careful consideration of various factors. These include the location and method of data storage, the metadata associated with it, data querying, access authorization, cost optimization, data auditing, and more. For simple applications with a single reader and writer, direct usage of Binary Large OBjects (BLOBs)…
-

Build vs Buy
And age-old question that is not really possible to settle. Should we the company build it? Or should we buy it? In general, I have a short set of questions that help to determine if it should be built, or if it should be bought: To expand on each of these as they can become…
-
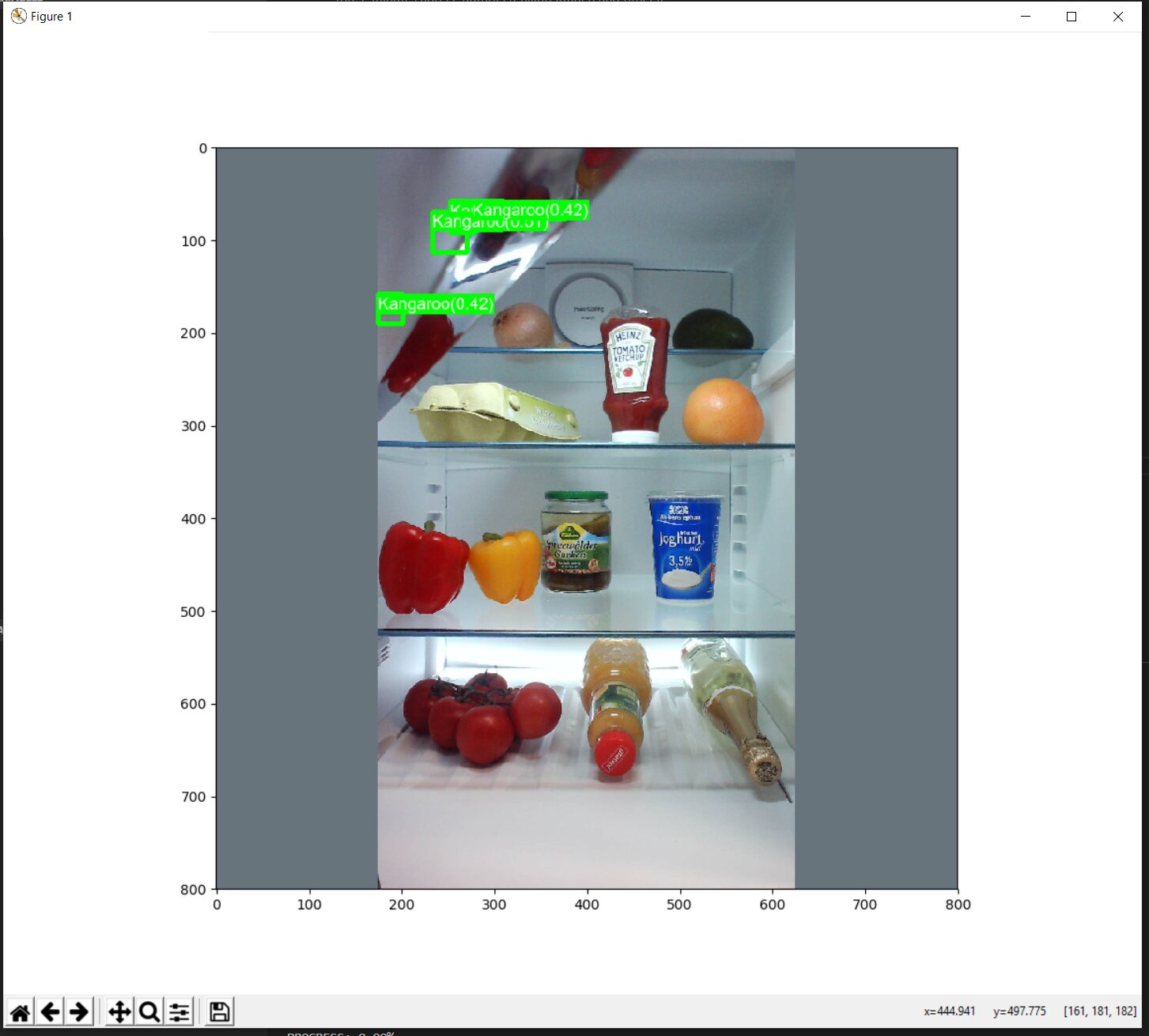
Kangaroos in my fridge! A Machine Learning Adventure
In 2018, as I embarked on my journey to develop machine vision models, I found myself working with a unique dataset – segmented images of kangaroos. My goal was to create a model capable of detecting and subsequently counting the number of kangaroos in a given region. The images I used were snapshots of the…
-

Unmasking Security Flaws: A Deep Dive into System Vulnerabilities and Misconfigurations
For some of my clients, I look at the software that they have had custom built and look at if it is “Fit for purpose”. One of my clients have very high security requirements, where they need to have the systems that they use be hardened and secured. This means that their internal systems are…